Cyber
Radiance applies our cyber capabilities in novel and unique ways to support the Intelligence Community, armed services, research laboratories, and test ranges. At our founding, we focused on performing vulnerability and capability assessments of complex weapon systems and their unique software and hardware. Over the last 20 years, we’ve expanded to include all aspects of cyber operations with a specialty in systems not covered by traditional cyber methods, tools, and techniques. These systems include weapon systems, critical infrastructure, electrical power systems, transportation systems, industrial control systems, and special purpose hardware and software. Across these domains, we leverage our employee-owner experts and decades of experience to keep America, our troops, and our citizens safe.
Hardware and Software Reverse Engineering
Radiance provides deep engineering expertise in hardware and software reverse engineering and exploitation for our clients. Our engineers find weaknesses that can be used as paths to defeat, exploit, and characterize Red Threat systems. We also conduct Blue systems vulnerability assessments to increase lethality and reduce exploitation risk. Our team technical expertise allows us to work on a broad portfolio of assets from lifted software code and binaries to complex current system. Our engineers play a critical part in providing forensic analysis from systems captured in the field that helps our clients build a greater understanding of our adversaries perceived versus actual capabilities.

Vulnerability Assessments
We perform detailed systems vulnerability assessments for our Government and commercial customers on operational technologies such as weapon systems, vehicles, and industrial control systems. Our assessments include a combination of on-site inspections, organizational procedures reviews, penetration testing, and reverse engineering key components. Our approach not only finds vulnerabilities at the subsystem level but develops an understanding of how they can propagate through a system of systems and whether they can impact the overall operation.
Exploitation Development
We discover, identify, detect, and analyze vulnerabilities in non-traditional systems. We then develop capabilities to exploit these vulnerabilities and generate payloads or implants for integration with access tools and platforms.

Protective Technologies
Our multi-discipline systems security experts assess architectures from the inside out, first evaluating components, platforms, network structure, and mission systems at multiple levels to fully assess the threat. Radiance’s unique expertise in microelectronics security, supply chain security, and trusted systems allows us to fully understand the risk to system critical program information (CPI) for weapons systems and platforms. Understanding these systems’ CPI allows us to apply our proven cyber-hardening techniques, guidance, technologies, and methodologies to ensure our customers’ most critical systems are protected against current and emerging threats.
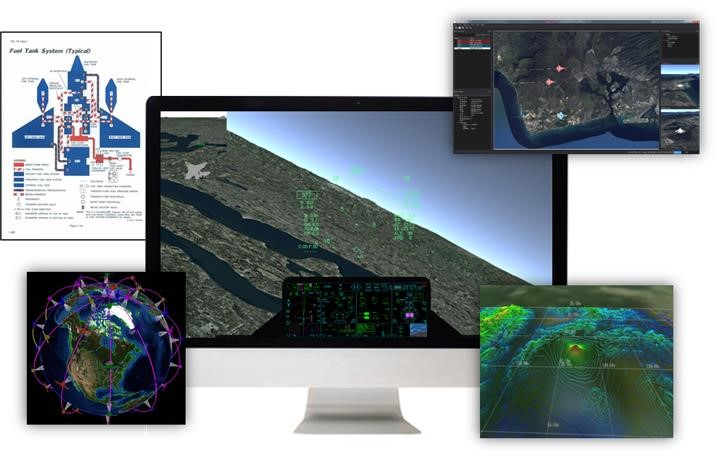
Modeling, Simulation, and Analysis
Radiance models, tools, and analysis capabilities have supported many virtual and open-air test events for the DoD. We’ve developed and employed high-fidelity modeling techniques that allow a cyber team to exploit system capabilities and vulnerabilities in a laboratory environment. In addition to cyber, our models support a variety of mission areas including electronic counter measures evaluation, electronic warfare, and country-level studies. We also provide innovative tools that allow for analysis and visualization of large amounts of engineering data generated during these evaluations.